The main questions here are – do people know what the EV certificate means? Does an EV certificate protect my business from online attacks?
The assumption is that if there is a “real name” inside a “certificate”, people will trust my web business more. Assuming they know what is my “name” and they know what “certificate” is. There are not very many of those!
Bottom-line is that you pay: $80+, you get: hard to put numbers on these things.
| Do you know what PKI is? Get one up and running in Amazon AWS with us – professional PKI system with secure hardware, setup in under 20 minutes. Dynamic domain name, HTTPS for its front-end, and FIPS140-2 Level 3 hardware. Give us thumbs up! |
 I personally like the green company name (instead of its internet address) that my iPhone shows when I go to a website with and EV certificate. However, this experience is not common (Enigma Bridge doesn’t have it), not even with big websites. What’s worse – even those I really trust – like Google, or Amazon.
I personally like the green company name (instead of its internet address) that my iPhone shows when I go to a website with and EV certificate. However, this experience is not common (Enigma Bridge doesn’t have it), not even with big websites. What’s worse – even those I really trust – like Google, or Amazon.
When I look back, the biggest problem of secure HTTPS websites was that people couldn’t tell the difference from unsecured websites. I believe, this is still a problem today and one of the reasons behind the Let’s Encrypt project. The other day, my wife was suspicious about a well-known online shop, which didn’t have the padlock in the address bar. However, inside the website, it had a big text box saying – your payment will be processed securely by <payment gateway>. Still, I prefer buying from main online shopping sites, because I know the brand and trust them. Having said that, most people look for a padlock in the address bar and become suspicious if it isn’t there.
Here comes EV certificate. Issuing certificates has become a commodity service. There is not real differentiator between provides, beside the price. So vendors came up with the idea of EV certificates to charge more per certificate, in exchange for “more thorough verification”.
Troy Hunt quite rightly says that these certificates contain information about the “legal entity” so we can learn more about who is behind the website. The certificate issuer will do 2 checks:
- that you own the domain name – they will ask you to put a particular file to your web site; and
- verify that your contact information is correct – they will call you and will try to find you in an online directory (Yell.com or similar).
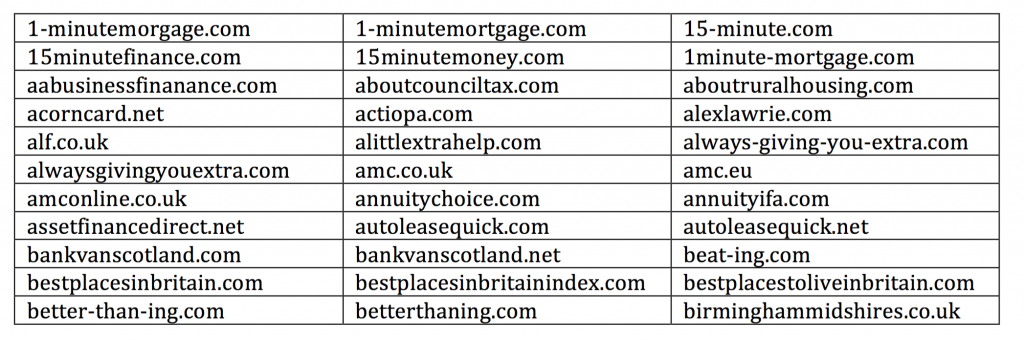
You think it’s easy to link those two checks together but it’s not the case. I would also argue that certificate owner information in the certificate doesn’t give much value either. You would be surprised, how many domains – and what are their names – are registered by big companies. Here’s a small subset of domains registered by Lloyds bank.
I believe that it is not the case that an EV certificate is going to increase the trust of a website visitors. This trust must be built over time and the means are the content of the website and relevant services.
What the SSL / HTTPS certificate should protect me from is someone hijacking my domain name and re-directing my customers to a rogue website. EV validation doesn’t improve my chances here and certificate vendors follow basically the same rules here as for the cheap non-EV certificates.
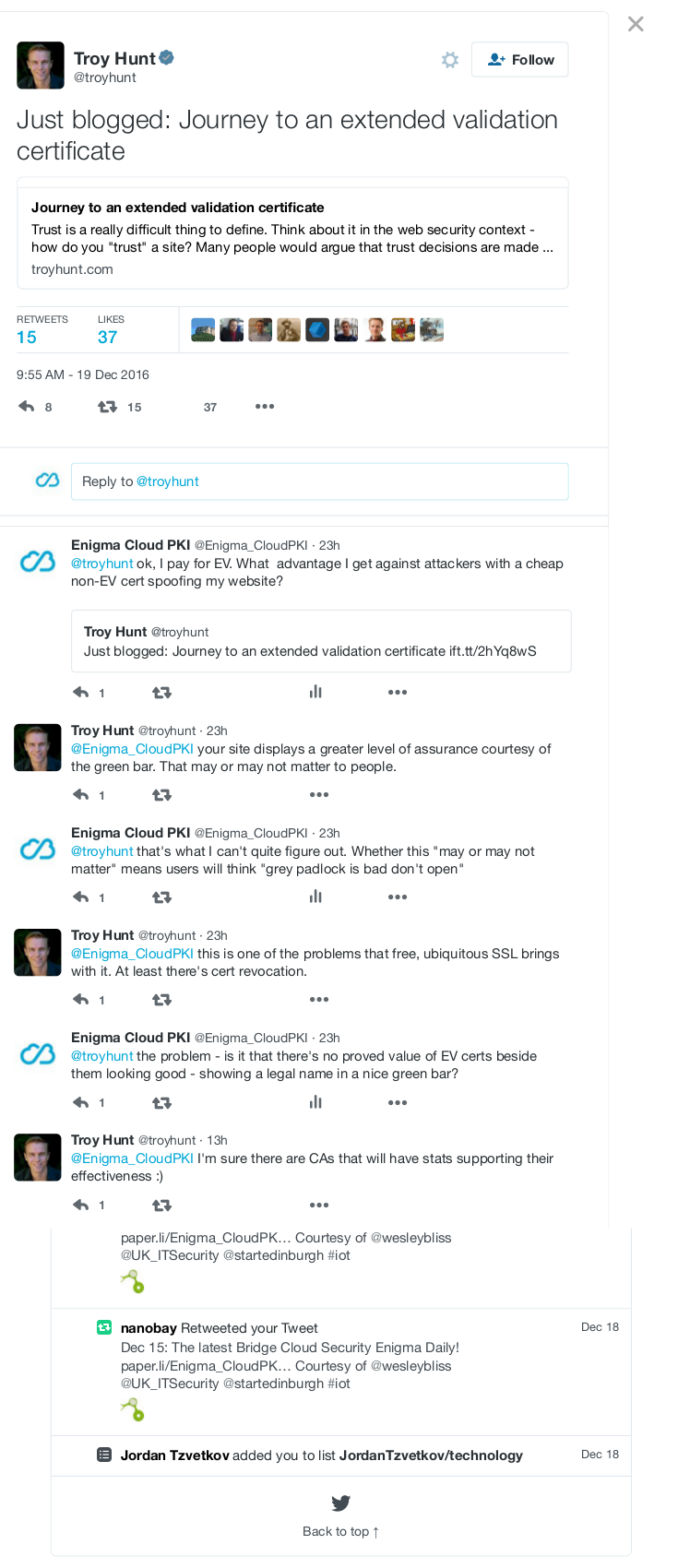
Despite me complaining about Letsencrypt domain validation, they do better job with domain validation than vendors issuing EV certificates. I tried to run my thoughts past Troy Hunt and here’s a transcript:
@troyhunt ok, I pay for EV. What advantage I get against attackers with a cheap non-EV cert spoofing my website
@Enigma_CloudPKI your site displays a greater level of assurance courtesy of the green bar. That may or may not matter to people.
@troyhunt that’s what I can’t quite figure out. Whether this “may or may not matter” means users will think “grey padlock is bad don’t open”
@Enigma_CloudPKI this is one of the problems that free, ubiquitous SSL brings with it. At least there’s cert revocation.
@troyhunt the problem – is it that there’s no proved value of EV certs beside them looking good – showing a legal name in a nice green bar?
@Enigma_CloudPKI I’m sure there are CAs that will have stats supporting their effectiveness 🙂
@troyhunt good to see someone who still upbeat! 🙂 I get EV auth. value if clients can enforce its use. But web threat model is ..wider.?.
@Enigma_CloudPKI yeah, it’s all very hard to define, I get that
@troyhunt not sure you’re contradicting your ehtusiasm for your new EV cert or not. Real security v PKI business model :/
@Enigma_CloudPKI not at all, just continually saying it’s hard to put numbers on these things