Unifying Let’s Encrypt and Long-term Certificates
Let’s Encrypt has a number of downsides when used on a large scale. It uses modern key management protocols, but the high-level of automation requires management. This is what KeyChest provides.
The “zero” cost of Let’s Encrypt certificates is balanced-out with two main downsides: rate limits and short lifetime of certificates. While it’s great to get a free product, it becomes somewhat dangerous when you start relying on it without giving a proper thought to what should happen in 3 months’ time when you need to renew it.
There is also an adoption barrier as Let’s Encrypt uses an automation for renewals (so called ACMEv2 standard) and it requires a complete change in the way you manage your certificates.
Nevertheless, Let’s Encrypt is a viable option for HTTPS and other encrypted internet services.
There are many instances where operational teams choose to deploy a Let’s Encrypt certificate when an important service went down due to an expired certificate or the time left is too short to follow usual purchasing. Now imagine you have hundreds such certificates – how can you keep on top of them all?
KeyChest is now testing (Dec 2019) a new proxy service, which provides a valuable information about the status of Let’s Encrypt certificates. The use requires a small change to the way you use KeyChest agents – Certbot by setting an HTTPS_PROXY. If your existing command is “certbot renew”, the new version would be:
“export HTTPS_PROXY=https://test.keychest.net:6443; certbot renew”
KeyChest will start logging all your requests and create statistics of your usages of Let’s Encrypt. You will instantly get information about the activity of your Certbot agents and detect issues when they happen – not when your certificates start expiring.
This also helps to comply with Let’s Encrypt rate limits, some of which are fairly strict:
- maximum of 5 new certificates per domain per week;
- 50 certificates per registered domain per week;
- 300 new “orders per account per 3 hours; or
- 5 failed validations per account per hour.
Deep Let’s Encrypt Proxy
While the monitoring will get you on top of your Let’s Encrypt usage and reduce the risk of downtimes. Our ambition is to unify ACME and “legacy” certificate issuers.
We achieve that with a deep proxy that does the actual communication with the Let’s Encrypt issuing servers and also validation challenges.
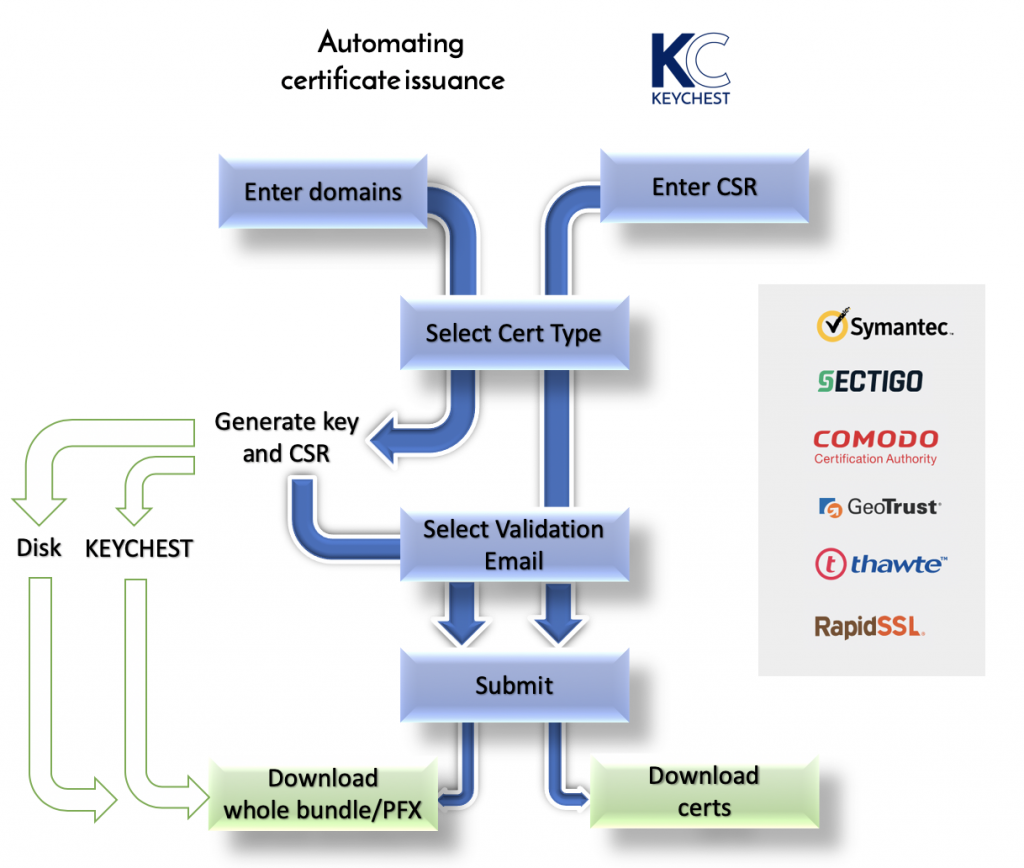
This allows us to forward certificate requests to Let’s Encrypt, Comodo, Symantec, … or any other certificate issuer according to your requirements. To further simplify your IT operations, our proxy architecture allows endpoint agents to be much smaller with fewer dependencies and installation issues.
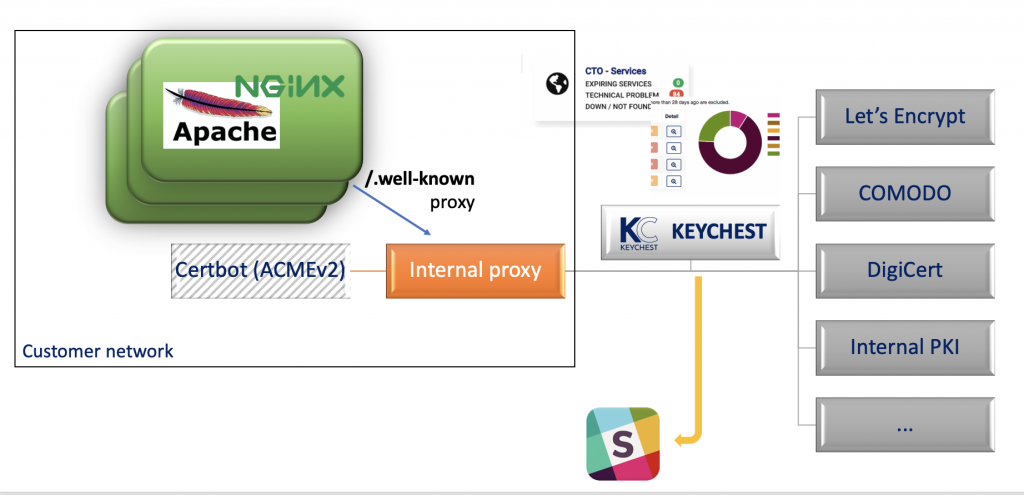
You can either forward (an HTTP reverse proxy) validation requests directly to the KeyChest service, or use our lightweight agents available to the Small Enterprise customers.
Many companies are considering switching to Let’s Encrypt. What we offer is a management service to keep your commercial certificates while simplifying the configuration of your servers and preventing downtimes.
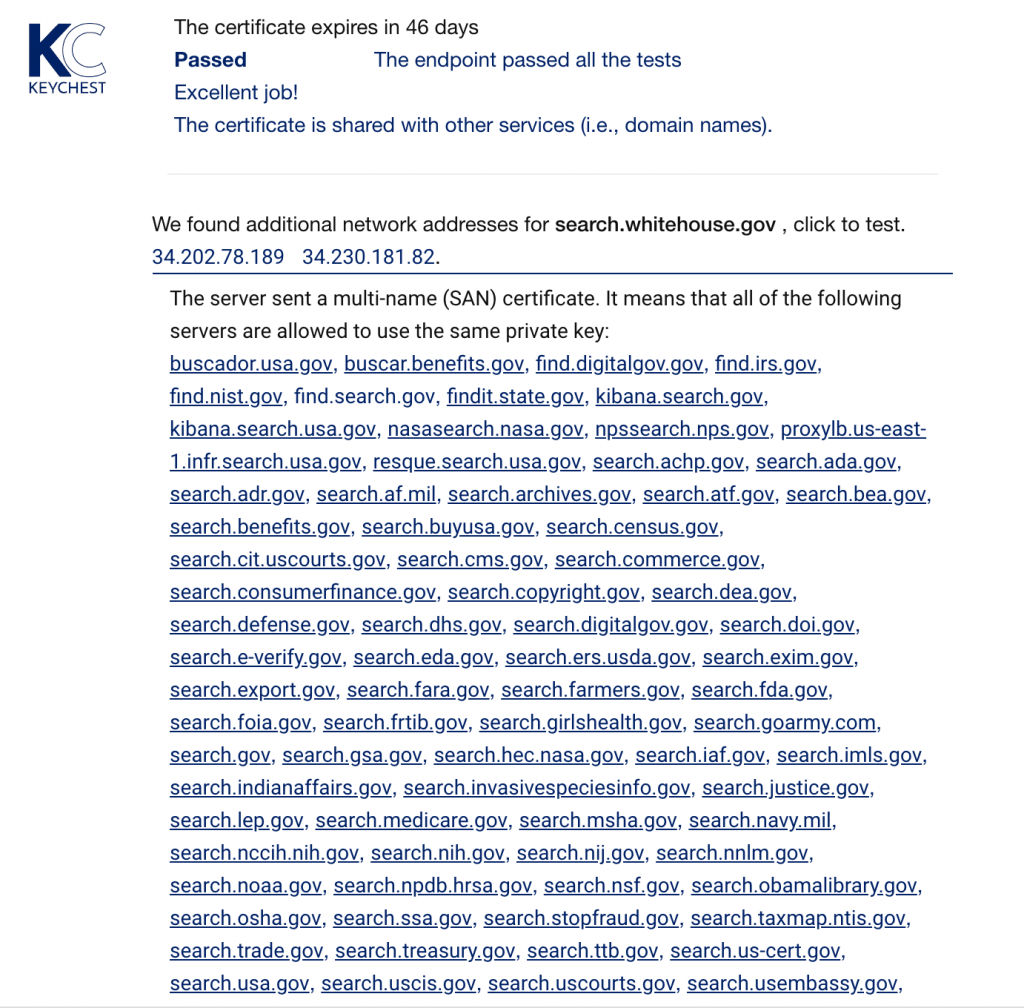
KeyChest has a complete database of all internet certificates and can automatically start monitoring any new servers and services you create – providing you with ongoing 100% coverage of your registered domains.