The main problem with smart cards is lack of secure display and keyboard that would allow users to verify data sent to the smart card from their computer. Malware on the computer may then alter the data and, for example, change the recipient of a bank transfer.
Smart cards are widely used to protect transactions carried out by users on their personal computers. Smart cards can implement cryptographically secure authentication and authorisation.
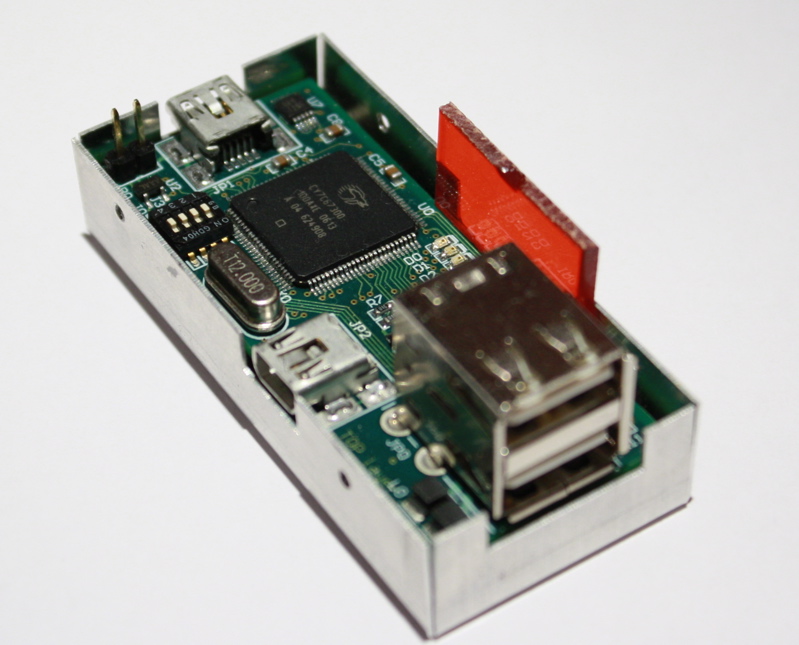
As part of a project for a client we have developed an architecture and implementation of a device allowing use of an additional device to display and confirm data sent to a smart card. The device connected to a computer USB port, a USB smart-card reader, and a third device connected via a USB port and an infrared channel. Our implementation operated in transparent mode so that no additional USB drivers were needed.
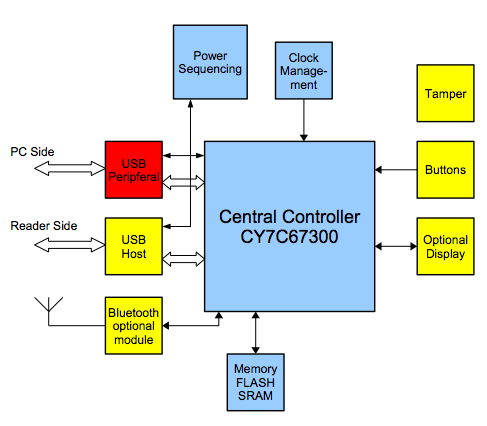
Our implementation operated in transparent mode so that no additional USB drivers were needed.
We have also produced a detailed analysis of security mechanisms used for payment transactions and a classification of attacks with their applicability on different authentication and authorisation protocols.
IBM has been offering a device built on similar principles with much improved design about 4 years later – ZTIC.
Thanks for sharing valuable content
Smartcards provide flexibility of secure transactions with unique identities at most worldwide locations. Security in applications and services is a matter of concern for any organization which is boosting the smart cards market globally.