Masaryk University has published a new cryptographic attack. You may still remember their ROCA attack from 2017. While ROCA was about the RSA encryption, MINERVA is about Elliptic Curve (ECC) signing.
It seems that the Minerva attack came to light when they were playing with old IDProtect Athena cards. They discovered a correlation between key lengths and timing. This allowed them to eventually recover the whole private key with relatively small number of signatures.
The details of the attack are available from https://minerva.crocs.fi.muni.cz/
CROCS Masaryk University
This original attack took around 30 minutes and it was using smartcards – that would not allow more than 10 signatures per second. Indeed, the number of operations required was around 11,000.
Athena SCS IDProtect used to be approved for use by the US government as PIV cards in 2008 but they are not really being sold any more. I would also expect only a low number to be still in use. … so possibly just of academic interest?
Expanding The Impact
While the impact of the original attack was small, they had a brilliant idea – what about testing the attack against software libraries. I would expect them to be quite surprised when they found quite a few, fairly popular libraries to be vulnerable.
- CVE-2019-15809: Vulnerability in Athena-based cards.
- CVE-2019-13627: Vulnerability in libgcrypt.
- CVE-2019-13628: Vulnerability in wolfSSL/wolfCrypt.
- CVE-2019-13629: Vulnerability in MatrixSSL.
- CVE-2019-2894: Vulnerability in SunEC/OpenJDK/Oracle JDK.
- CVE-2019-14318: Vulnerability in Crypto++.
Most of them have been fixed in upgrades over the summer, but I’m pretty sure that there will be zillions of projects that will rarely upgrade versions of cryptographic libraries. So the impact may be long-term with smaller attacks to keep coming over many coming years.
Humble Beginnings
I am personally amazed by the results Petr Svenda et al achieved in the last few years. Especially when I remember the beginnings of the timing analysis research that I started back in 2002/3 by designing an analytic toolkit for timing and power analysis of smartcards.
It took a while, but I found a couple of pictures in ancient backups of my laptops that reminded me of the sleepless nights when I tried to get the firmware to measure instead of to burn smartcard chips.

At the time I thought that just the timing attack has been a bit lame and we really needed to combine it with power / glitch attacks. The SCSAT tools were designed to generate microsecond, high voltage peaks on power, clock, and data pins of smartcards. The goal was to induce computational errors without triggering protection mechanisms of smartcards.
Anyway – the main memory of mine is of long hours of work and it’s absolutely amazing that what I have started many years ago has been turned into absolutely fascinating results by Petr Svenda and his team.
SCSAT Specs
“It all may seem to be just a game but these techniques may be used for discovering private keys used by smart-cards for signing e.g. your payment orders when using internet banking.”
Download
I’m sure you will be able to read details of the attack elsewhere, so I will just add here a short spec I’ve written about 10 years ago 🙂
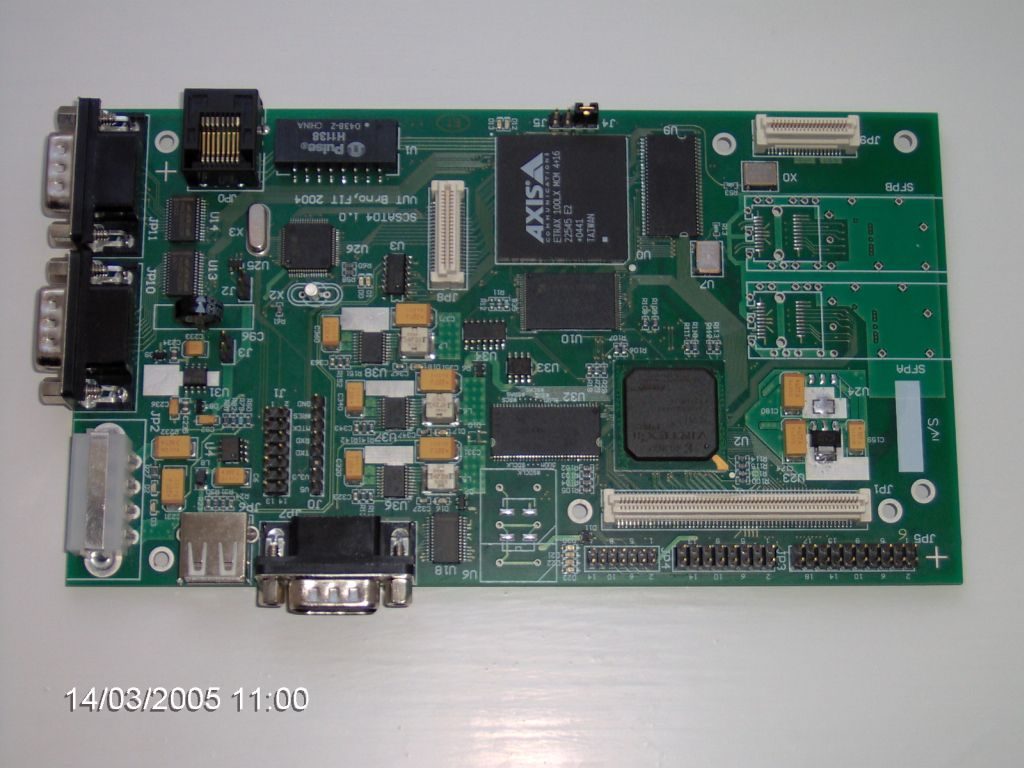
We have designed and developed a purpose-built device (SCSAT02, followed by a more powerful SCSAT04) for side-channel attacks on microcontrollers (the hardware implementation was delivered by the DFC Company. The primary focus of SCSAT04 was an analysis of smart-card robustness against side-channel attacks like power analysis, (simple and differential), or fault/glitch attacks (via manipulation of power supply, external clock signal, data bus voltage).

The device has been used for analysis of the Java Card security, especially with respect to side channel attacks on Java applets – some measurement traces and results can be found in a paper from Masaryk University in Brno.
The SCSAT04 system, targeted high volume data analysis, is built around ETRAX100LX processor and Xilinx II Pro programmable gate array with builtin PowerPC 405 core.
- ETRAX 100LX MCM processor
- ethernet 100Mbit, USB, RS232
- 32MB SDRAM, 12MB flash
- Virtex II Pro XC2VP7@5-7 gate array
- OS Linux for PPC in FPGA available
- partial reconfiguration and debugging readback over JTAG bus supported
- DDR 64MB@100 / 133MHz – 16bit connected to FPGA
- FW/HW data analysis acceleration inside FPGA
- 2 x RS232 port for FPGA
- DataFlash Card
- upto 200MHz/12bit sample rate
- 2 * 100MHz waveform generators