I will soon blog more details about our talk at DEFCON, where we did a live demo of our multi-party encryption system, aka, secure encryption when everything is hacked or back-doored (an initial info is at https://enigmabridge.com/mpc).

This time, I will focus on the hardware platform, we developed for smart cards and which we utilized for the projects we recently presented. This is the hardware, which powers our cloud encryption service. It is meant as an un-trusted communication layer for smart cards as it does exactly that – makes smart cards available via the TCP/IP protocol.
While we believe smart cards provide an incredible computational power (especially for cryptography) per Watt of energy, their use is restricted by existing smart-card readers. We needed something that would be reliable, give us enough control over smart cards, i.e., control on the physical layer, and we also needed scalability – being able to connect thousands of smart cards to a single Linux “controller”. So we designed Simona boards.

Simona board is simply a device, which converts the half-duplex serial protocol (ISO7816) to TCP/IP. We assumed that TCP/IP clients connecting to smart cards would be more reliable than USB or any other smart card readers and over two years of experience have proved us right.
DEFCON-25, Track 2, 29th July @2pm – “Trojan-tolerant Hardware & Supply Chain Security in Practice“. The talk included a live demo of multi-party encryption to keep you secure even when your processors are hacked. Short demonstration videos and a summary at https://enigmabridge.com/mpc
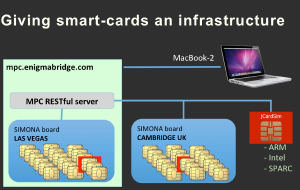
We have used Simona boards to implement and successfully demonstrate a set of multi-party crypto (MPC) protocols at DEFCON-25, including a combination of Simona boards in the room and in our Cambridge office, some 5,000 miles away. Our goal was to show that it was possible to implement cryptographic protocols on devices with completely disjoint manufacturing processes – from design, chip manufacturing, firmware, all the way to products on your desk.
We needed to overcome certain difficulties with ECC (elliptic curve cryptography) and we announced an open-source library at BlackHat USA 2017.
Well, what I wanted to present here were some great statements we received from ACM Computer and Communications Security (CCS) reviewers. The ACM CCS conference being one of the best research IT security conferences around.
Scalability and practicality:
The idea to prototype this [MPC protocols] on JavaCards is nice, they have a high level of compatibility between manufacturers and this allows to efficiently distribute such computations across multiple devices, in a very realistic setting. In fact, the prototype as it is now could find some practical uses.
Security of the system
It’s a very good try to apply distributed cryptographic techniques into building a trusted hardware. Through using this technique, plaintext in one IC cannot be revealed by any other ICs in the system. So that only if all the ICs are taken over by the attacker, the confidentiality and the integrity of the Myst [MPC system] can be broken.
and
Nevertheless, it looks like the proposed solution gets the job done: the system remains secure as long as at least a single among “k” ICs is non-compromised.
and its potential
Myst [MPC protocols] is a very inventive combination of advanced crypto techniques and fault tolerant system design. I like that Myst has the potential to address leakage problem (one of the easier attacks to implement, but hardest to defend against).
If you’re keen to see the full, final proposition, come to Texas, Dallas at the end of October, when we present the system at the ACM CCS conference, the flagship annual conference of the Special Interest Group on Security, Audit, and Control (SIGSAC) of the Association for Computing Machinery (ACM).