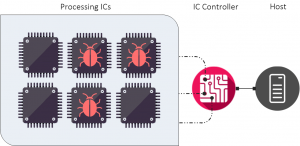
Multi-party encryption protocols require a number of parties to co-operate to produce a valid digital signature, or to retrieve encrypted data. The implementation we developed with University College London allows customers to mitigate threats of bugs on the processor level (the most recent incident affected a whole range of Intel processors).
While our protocols have unique security properties, they are also practical and can be used in a number of use-cases. Just digital signing is used in a number of applications – from code-signing to validating legal documents (especially in the EU).
The simplest implementation would involve just two parties – a cloud service of the key owner. The key owner can be a developer responsible for publishing new versions of an app, or a member of a company’s board of directors, who needs to sign collective resolutions.
As the cloud service is needed for signing, but it can’t sign on its own, the developer and the director keep their “sole ownership” of their key. At the same time, they can use the cloud service to help them mitigate damage if their laptop, or mobile phone is stolen or compromised.
This is the key property of multi-party cryptography we implemented. If you have a key in 10 parts, you need all the parties to co-operate. But any 9 of the 10 will gain nothing if they collude trying to compromise the signing / decryption key. As long as there is one last standing, the key itself is secure. It means that if just one part of the key is protected by secure hardware or any particular security mechanism you can think of, it will define the security of the whole key. The strongest security provided to any of the key parts will dictate the security of the key.
That gives as the right to claim that our protocols are very flexible in terms of the cost versus security.
The way we have implemented the set of protocols creates a unified platform for fast and low-security software implementations (depending on the distribution of the control over key parts) as well as high-assurance implementations with processors providing an additional layer of physical security for key parts.
The beauty of the protocols is that they are as secure as the most secure part of the key. A complete opposite of the usual expectation of the chain being as weak as the weakest link.
See as at DEFCON 25 or read more at the Business Weekly newspaper. We will publish details after DEFCON and BlackHat USA.