We have started testing our SSL certificate spot checks – KeyChest – and realized that we were conceptually different from SSL Labs. We focus on the server rather than the domain name and it makes a difference.
Category Archives: https
SSL certificates – 7 Free Spot Checks in one go – KeyChest
While implementing features of the certificate planner, we have added a few handy features to the KeyChest spot checker as well. It is now much more than just a tool to check when a website certificate expires.
Continue reading SSL certificates – 7 Free Spot Checks in one go – KeyChest
Meet your internet neighbors – sharing SSL keys with strangers
You may think I’m pulling your leg, when I say that you share encryption keys with an adult content website, road sweepers West Sussex, or hackers trying to impersonate Apple. But that’s exactly what happens when you use a free (CDN) service with HTTPS.
Continue reading Meet your internet neighbors – sharing SSL keys with strangers
KeyChest – FREE plan and track for 100% HTTPS uptime
We have been using Letsencrypt certificates for a year now. As it is free, we have been constantly increasing the number of services using it. I personally like the three months validity as it makes renewals a “business as usual” task, rather than incidents. But it doesn’t happen through magic.
Continue reading KeyChest – FREE plan and track for 100% HTTPS uptime
EV Certificates – Value for Money? Incl. Troy Hunt Q&A
I have come across Troy Hunt’s article yesterday about getting an EV certificate. His initial assumption is that EV certificate actually proves something, unlike many other seals of “security”. But is it really worth spending $80+/year?
Continue reading EV Certificates – Value for Money? Incl. Troy Hunt Q&A
How Certbot and Letsencrypt Work (DNS and SNI-TLS automation)
We introduce an integration plugin for Let’s Encrypt. It provides integration for a variety of mechanisms that enable and simplify verification of domain control and certificate installation. We already tested it with Dehydrated (former letsencrypt.py) . It supports all existing verification methods: DNS, HTTP and TLS-SNI, in their current versions “01”.
Continue reading How Certbot and Letsencrypt Work (DNS and SNI-TLS automation)
Your HTTPS Certificate Shows Where Its Key Comes From
We have extended the original research and can now use information from public keys (HTTPS, TLS, SSH, SSL) to audit cyber security management and compliance with internal standards.
Continue reading Your HTTPS Certificate Shows Where Its Key Comes From
Letsencrypt’s Vulnerability Or Feature – Eternal Account Key
The growth of Let’s Encrypt is phenomenal – 7 million certificates in last four months. The remaining hurdle for automation is verification of domain ownership. Well, actually it is NOT true. We were doing syntax testing – hoping to get the right kind of verification error … only to discover we have been successfully verified without providing any information.
Continue reading Letsencrypt’s Vulnerability Or Feature – Eternal Account Key
Re: Investigating the Origins of RSA Public Keys
This post is about a research done by one of our co-founders. Petr showed that it is possible to find which tool or hardware device generated RSA keys from just a few public keys. I’m thinking it’s an attack, unexpected data leakage channel, but also an excellent source for audit-related analytics.
Continue reading Re: Investigating the Origins of RSA Public Keys
“One time passwords” are not passwords
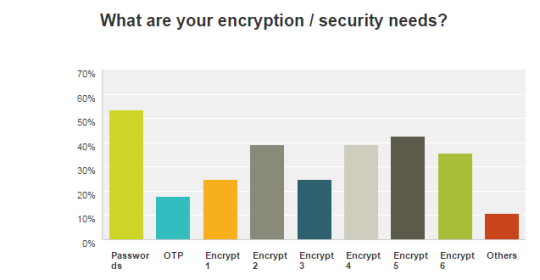
We did a bit of research into what IT start-up companies need in terms of security. I did expect that secure authentication / logons would be at the top but I was surprised that OTP (one time passwords) were at the bottom.